If you have spent any time in cybersecurity, you have probably heard the phrase, "It is not a matter of if you will be breached, but when." While it sounds a bit dramatic, it carries a painful truth. Sophisticated adversaries - from state-sponsored groups to financially motivated criminals - regularly bypass traditional security controls. Firewalls, antivirus engines, and even next-gen endpoint solutions catch a lot, but they do not catch everything. That gap between what your automated tools detect and what actually exists in your environment is exactly where threat hunting lives.
In our day-to-day work as a threat intelligence team, we spend a significant portion of our time not just collecting indicators of compromise and writing detection rules, but actively digging through networks, logs, and endpoint data for signs of malicious activity that nobody - and nothing - has flagged yet. In this post, we want to share what threat hunting really looks like in practice, why it matters, and how your team can start doing it effectively.
| Metric | Value |
|---|---|
| Avg. days to identify a breach | 194 |
| Breaches involving human element | 68% |
| Breaches discovered via third-party | 53% |
| Faster detection with active hunting | 6× |
Those numbers paint a clear picture: automated detection alone is not cutting it. Organizations that actively hunt for threats in their environments find adversaries significantly faster, contain damage earlier, and reduce the overall cost of incidents by a wide margin.
01 - What Is Threat Hunting, Exactly?
Threat hunting is the practice of proactively searching through networks, endpoints, and datasets to detect threats that have evaded existing security solutions. Unlike traditional detection - where you set up rules and wait for alerts - hunting flips the model entirely. You start with a hypothesis, a suspicion, or an intelligence lead, and you go looking for evidence.
Think of it this way: your SIEM, EDR, and firewall are like security cameras. They watch specific angles and alert you when something crosses a predefined threshold. Threat hunting is the security guard who actually walks the floors, checks the locked doors, and looks behind the shelves - places the cameras simply do not cover.
Key Distinction
Threat hunting is not the same as incident response. Incident response begins after a detection or a confirmed event. Threat hunting happens before any alert fires - its entire purpose is to find the things that your detections missed.
Reactive Detection vs. Proactive Hunting
| Aspect | Reactive Detection | Proactive Hunting |
|---|---|---|
| Trigger | Alert or signature match | Hypothesis or intelligence lead |
| Approach | Wait for notification | Actively search |
| Coverage | Known threats, written rules | Unknown threats, behavioral anomalies |
| Speed | Depends on rule quality | Depends on hunter skill |
| Outcome | Incident ticket | New detection rules and intelligence |
| Human Role | Analyst reviews alert | Analyst drives the entire process |
02 - The Threat Hunting Process
While every organization adapts the process to fit its own environment, the core threat hunting workflow generally follows a consistent pattern. We typically break it down into six stages:
Threat Hunting Lifecycle: Hypothesize → Collect → Analyze → Validate → Respond → Document

Stage 1 - Hypothesize
Every hunt begins with a question. A good hypothesis is not random; it is grounded in threat intelligence, recent attack trends, known adversary behaviors, or gaps in your current detection coverage. For example: "Our environment uses PowerShell extensively. Could an attacker be abusing encoded PowerShell commands to execute payloads without triggering our current rules?" That is a clear, testable hypothesis.
Good sources for generating hypotheses include threat intelligence reports, MITRE ATT&CK framework techniques, recent vulnerability disclosures relevant to your stack, anomalies noticed during routine monitoring, and plain old experience-based intuition.
Stage 2 - Collect Data
Once you have a hypothesis, you need the right data to test it. This typically means pulling from endpoint telemetry (process creation logs, file modifications, network connections), network flow data, authentication logs, DNS query records, and cloud audit trails. The quality of your hunt is directly tied to the quality and completeness of your data. If you do not have visibility into certain areas of your environment, that is both a hunting limitation and a finding in itself.
Stage 3 - Analyze
This is where the real work happens. Analysts examine the collected data for patterns, anomalies, and indicators that align with the hypothesis. Techniques used here include statistical baselining (what does "normal" look like for this activity?), stack counting (how common is this behavior across all endpoints?), temporal analysis (when does this activity occur and does the timing make sense?), and relationship mapping (which entities are connected to the suspicious activity?).
Stage 4 - Validate
After you find something interesting, you need to determine whether it is genuinely malicious or a false positive. This stage involves deeper investigation - checking additional data sources, correlating findings, and sometimes working directly with system owners to confirm whether an activity is authorized.
Stage 5 - Respond
If the finding is confirmed as malicious, the hunt transitions into response mode. The affected systems need to be contained, the scope of the compromise assessed, and remediation steps executed. This is where hunting and incident response naturally intersect.
Stage 6 - Document and Improve
This is arguably the most valuable stage and the one most often skipped. Every hunt, regardless of whether it finds something malicious, should produce output: new detection rules, updated baselines, refined hypotheses for future hunts, and documentation that helps the next analyst build on your work.

03 - Hunting Maturity: Where Does Your Team Stand?
Not every organization is ready to jump straight into advanced threat hunting. The Hunting Maturity Model, originally proposed by David Bianco, provides a useful framework for assessing where your team currently sits and what you need to reach the next level.
| Level | Name | Description |
|---|---|---|
| Level 0 | Initial | Relies entirely on automated alerts |
| Level 1 | Minimal | Can use tools shared by others |
| Level 2 | Procedural | Follows defined hunting playbooks |
| Level 3 | Innovative | Original procedures, hypothesis-driven |
| Level 4 | Leading | Custom tooling, automated hunts, TI-driven |
Most organizations fall somewhere between Level 0 and Level 2. There is nothing wrong with that - the important thing is knowing where you stand so you can take realistic, incremental steps forward. If your team is at Level 0, jumping to Level 4 overnight is not realistic. Focus on building foundational data collection and getting comfortable with basic querying first.

04 - MITRE ATT&CK: The Hunter's Map
If you are doing any form of threat hunting in 2026 and you are not referencing the MITRE ATT&CK framework, you are working harder than you need to. ATT&CK is a living knowledge base of adversary tactics, techniques, and procedures observed in real-world attacks. It gives hunters a structured way to think about what adversaries do and how they do it.
We map every hunt to specific ATT&CK techniques. This ensures hunts are focused on real-world adversary behavior rather than theoretical edge cases. It allows teams to track which techniques have been covered and which remain blind spots, and it creates a common language when communicating findings across departments.
Commonly Hunted ATT&CK Techniques
| Technique | ID | Coverage |
|---|---|---|
| Command & Scripting Interpreter | T1059 | 92% |
| Scheduled Task/Job | T1053 | 78% |
| Application Layer Protocol | T1071 | 71% |
| OS Credential Dumping | T1003 | 67% |
| Indicator Removal | T1070 | 59% |
05 - Practical Hunting Techniques
Theory is important, but let us get into what hunting actually looks like when you sit down and do it. Here are some of the techniques that consistently deliver results in the field.
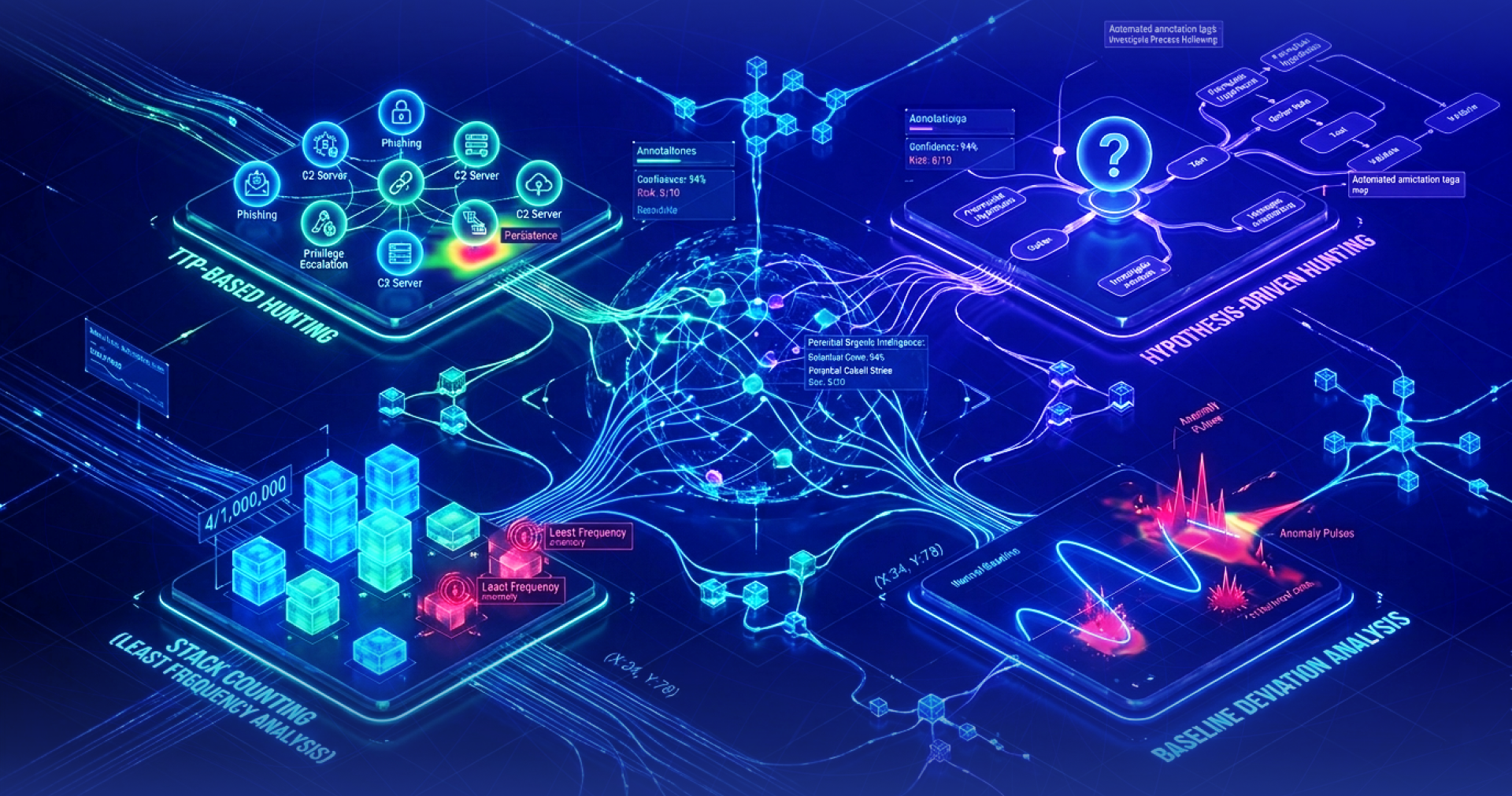
Stack Counting (Least Frequency Analysis)
This is one of the simplest and most effective hunting techniques out there. The idea is straightforward: count how many times a specific event occurs across your environment, then focus on the least common occurrences. Attackers often stand out not because their actions look obviously malicious, but because their actions are rare. If 500 endpoints run svchost.exe from C:\Windows\System32\ and one runs it from C:\Users\Temp\, that outlier deserves a closer look.
Hypothesis-Driven Hunting
As described earlier, this approach starts with an intelligence-informed hypothesis and systematically tests it against available data. For example, after reading a report about a threat actor using DLL side-loading with a specific legitimate application, you would search your environment for instances of that application loading unexpected DLLs.
TTP-Based Hunting
Rather than searching for specific IOCs (which change frequently), this approach hunts for the behaviors - the techniques - that adversaries use. Credential dumping, lateral movement via WMI, data staging before exfiltration - these TTPs remain relatively stable even as the specific tools and file hashes change from campaign to campaign.
Baseline Deviation Analysis
Establish what "normal" looks like for a particular data set - network traffic volume at certain hours, typical process trees on workstations, usual authentication patterns - and then look for deviations. This requires having solid baseline data, which is exactly why consistent logging and data retention are so foundational.
Common Mistake
One of the most frequent mistakes we see is teams trying to hunt without adequate data. If your logging is inconsistent, if key telemetry sources are missing, or if your data retention window is too short, even the best hunter will struggle. Invest in data collection before investing in advanced hunting capabilities.
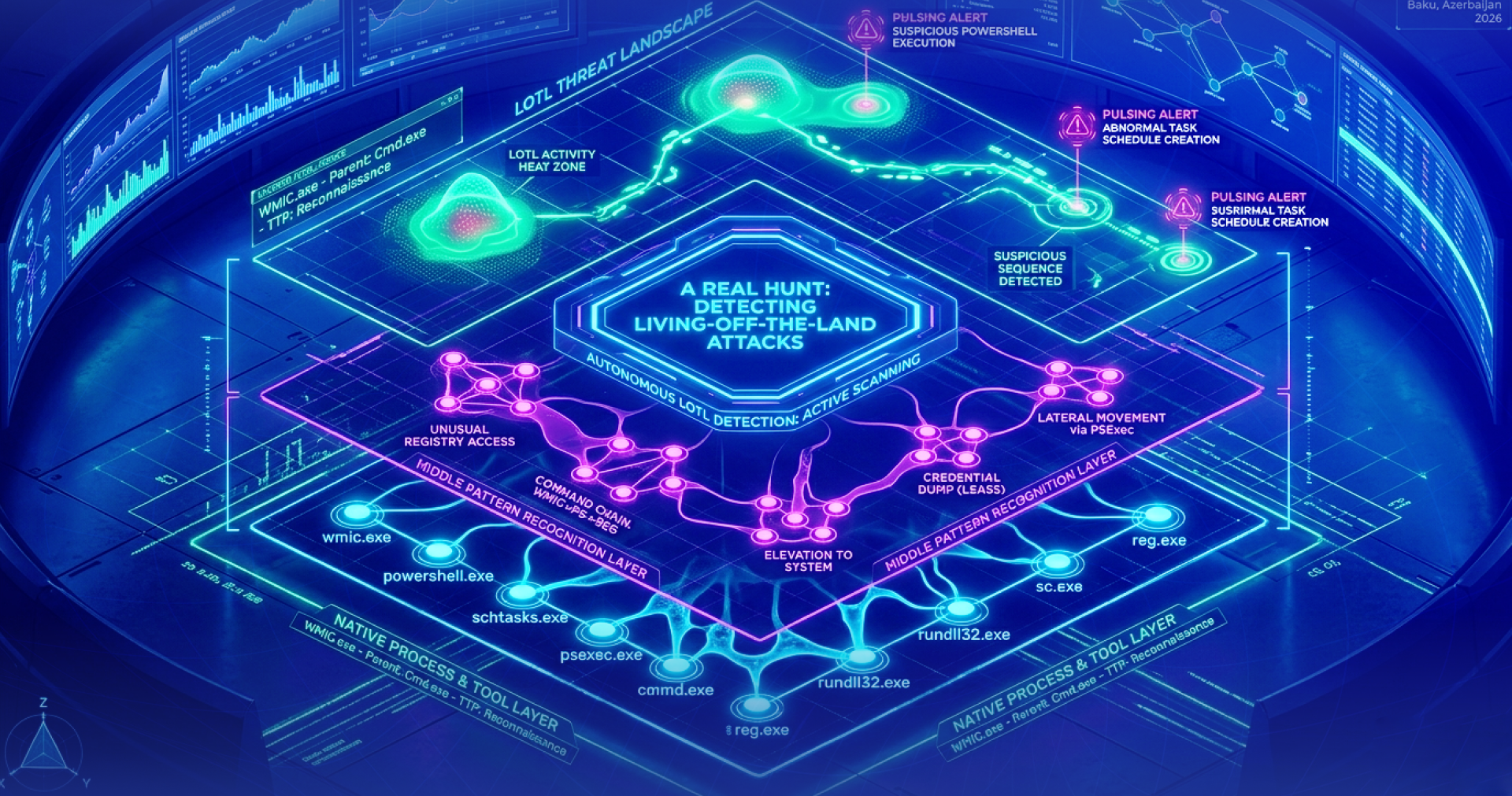
06 - A Real Hunt: Detecting Living-off-the-Land Attacks
Let us walk through a simplified version of a real-world hunt. Living-off-the-Land (LotL) attacks are among the most challenging to detect because the attacker uses legitimate system tools - PowerShell, WMI, certutil, mshta, bitsadmin - to carry out their objectives. No custom malware to signature, no suspicious binaries to flag.
Hunt Timeline - LotL Detection
| Phase | Details |
|---|---|
| Hypothesis Formed | Threat intelligence indicated that a specific APT group targeting the client's industry was leveraging encoded PowerShell and certutil for payload delivery. The hypothesis was that this behavior could exist undetected in the environment. |
| Data Collection & Analysis | We queried 90 days of process creation logs for all instances of PowerShell with -EncodedCommand or -e flags, and all certutil -urlcache executions. Stack counting revealed three endpoints with encoded PowerShell commands that did not match any known administrative scripts. |
| Validation | Decoding the Base64 commands revealed a downloader script pulling a second-stage payload from a compromised external domain. The certutil activity on one endpoint showed file downloads that were subsequently moved to a staging directory. |
| Outcome | The activity was confirmed as malicious. Compromised endpoints were isolated, credentials rotated, and the external domain blocked. Four new detection rules were written. Total dwell time before discovery: roughly 47 days - with zero alerts triggered by existing detections during that entire period. |
This case is a textbook example of why proactive hunting matters. The attacker had been operating in the environment for 47 days, using only legitimate tools, generating no alerts whatsoever. Without the hunt, discovery would have come much later - likely after the attacker had already achieved their objective.
07 - Essential Tools for Threat Hunters
Good hunters need good tools. The specific toolset varies by environment, but here are the categories and some tools that consistently prove their worth across different setups:
| Tool | Type | Description |
|---|---|---|
| Elastic / ELK Stack | Open Source | Log aggregation and analysis. Solid for large-scale querying and visualization of security events across the environment. |
| Velociraptor | Open Source | Endpoint visibility and forensic collection. Lets you run targeted queries across thousands of endpoints at the same time. |
| YARA Rules | Open Source | Pattern matching for files and memory. Essential for identifying malware families and suspicious file characteristics during hunts. |
| Sigma Rules | Open Source | Generic detection format that translates across SIEM platforms. Very useful for turning hunt findings into detection rules. |
| CrowdStrike Falcon | Commercial | Advanced EDR with powerful querying capabilities. Provides deep endpoint telemetry for endpoint-focused hunts. |
| Microsoft Sentinel | Commercial | Cloud-native SIEM with KQL-based hunting queries. Strong integration with Azure and Microsoft 365 audit logs. |
08 - Building a Threat Hunting Program
If you are looking to start or improve threat hunting at your organization, here is a practical approach based on what we have seen work across various industries and maturity levels:
- Start with your data. Audit what telemetry you currently collect. Identify critical gaps - if you do not have process creation logs, DNS query logs, or authentication events, address those first. You cannot hunt in the dark.
- Define your scope. You do not need to hunt across everything at once. Start with your most critical assets or highest-risk segments. A focused hunt that covers your crown jewels is far more valuable than a shallow sweep of everything.
- Use intelligence to drive hypotheses. Subscribe to threat intelligence feeds relevant to your industry. Read adversary reports. Track which threat actors target organizations like yours and map their known TTPs to your detection coverage.
- Establish a cadence. Threat hunting should not be a one-time event. Whether it is weekly, biweekly, or monthly, set a regular schedule. Consistency builds skill and ensures continuous coverage.
- Invest in your people. Tools matter, but the analyst behind the keyboard is what makes hunting work. Train your team on log analysis, forensics, scripting, and adversary emulation. Hands-on experience will always outweigh certifications.
- Document everything. Every hunt should produce a report - what was hypothesized, what data was examined, what was found or not found, and what actions were taken. This documentation feeds future hunts and strengthens overall detection posture.
- Close the loop. When a hunt reveals a detection gap, write a new rule. When it reveals a misconfiguration, fix it. When it reveals new attacker behavior, share that intelligence. Hunting should make your entire security operation better, not just produce one-off findings.
09 - Common Pitfalls to Avoid
Over the years, we have seen teams fall into similar traps when getting their hunting programs off the ground. Being aware of these can save you real time and frustration.
Hunting without a hypothesis. Randomly browsing logs is not hunting - it is exploring. While aimless exploration can occasionally turn something up, structured hypothesis-driven hunting is far more efficient and repeatable.
Chasing IOCs instead of TTPs. Indicators of compromise like file hashes, IP addresses, and domains have short shelf lives. Adversaries rotate them constantly. Techniques and behaviors persist much longer. Focus your hunts on how attackers operate, not the specific artifacts they leave behind.
Ignoring false positives. When a hunt turns up activity that looks suspicious but turns out to be legitimate, do not just dismiss it. Understand why it looked suspicious and document the legitimate explanation. This reduces noise in future hunts and may reveal policy violations or misconfigurations worth addressing on their own.
Working in a silo. Hunters who work without communicating their findings to detection engineers, incident responders, and the broader security team are leaving value on the table. The strongest hunting programs have tight feedback loops with other security functions.
10 - The Future of Threat Hunting
Threat hunting is evolving fast. Several trends are shaping what the discipline will look like over the next few years, and they are worth paying attention to.
Machine-learning-assisted hunting is becoming increasingly practical. ML models can process massive datasets, flag anomalies at scale, and surface patterns that human analysts might miss. That said, ML is a force multiplier, not a replacement. The human analyst remains essential for forming hypotheses, contextualizing findings, and making judgment calls that no algorithm can reliably handle.
Cloud-native hunting is now a necessity rather than an afterthought. As workloads move to cloud environments, hunters need to be comfortable with cloud audit trails, container logs, serverless function activity, and IAM-related events. The attack surface has expanded, and hunting practices have to keep up.
Collaborative intelligence sharing is becoming more structured and more valuable. Organizations participating in ISACs, contributing Sigma rules, and feeding into open threat intelligence platforms create a collective defense that benefits everyone involved. Adversaries collaborate - defenders must do the same.
Automation of routine hunts is freeing up skilled analysts for more complex, creative work. Hunts that have been validated and documented can often be converted into automated, scheduled queries that run continuously in the background. This lets human hunters focus their energy on novel hypotheses and advanced adversary tactics where they add the most value.
Final Thought
Threat hunting is not about having the most advanced tools or the biggest team. It is about cultivating a mindset - the willingness to question assumptions, the discipline to follow a structured process, and the persistence to keep looking when everything appears normal. In cybersecurity, "everything looks fine" is sometimes the most dangerous signal of all.
If your organization is thinking about building a threat hunting capability, developing hunt hypotheses tailored to your threat landscape, or conducting managed hunting operations - start small, stay consistent, and never stop asking questions. That is where the real value lives.